The Network Problems Most Businesses Don't See
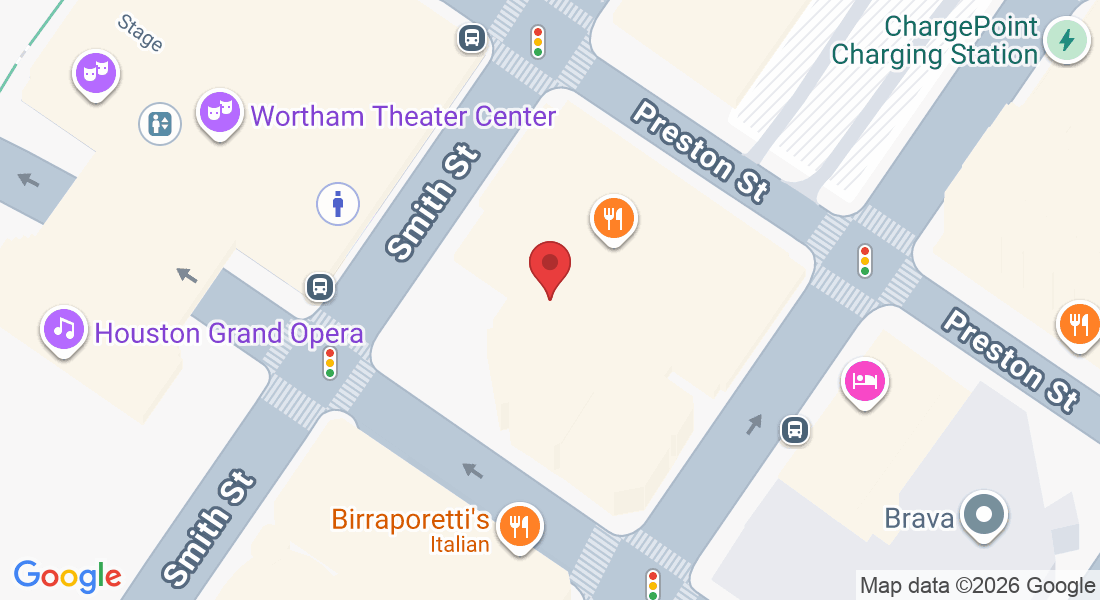
Most Houston businesses don't realize their network has vulnerabilities until something goes wrong. Slow performance, dropped connections, and unauthorized access often share the same root cause: infrastructure that was never properly configured or monitored.
A poorly managed network doesn't just frustrate your team. It creates gaps that attackers actively look for, and for businesses handling sensitive client data, those gaps carry compliance consequences that go well beyond the cost of an IT repair call.
What We Do For You...
Continuous monitoring catches threats and issues before they escalate
Your infrastructure is configured for both operations and compliance
Unauthorized access attempts are detected and blocked at every entry point
Remote and on-site users connect securely without exposing sensitive systems
Network performance is optimized so your team works without interruptions
Firewall rules, access controls, and segmentation are regularly maintained
Every layer of your infrastructure is documented, monitored, and aligned
Our Cybersecurity Track Record is Our Best Asset
Our Clients' Confidence Is The Only Proof We Need
How We Strengthen Network Reliability For You
Our management approach improves stability, strengthens performance, and reduces disruptions by combining visibility, monitoring, optimization, and aligned support. These elements work together to keep your environment dependable, efficient, and ready for growth.
Focused Visibility Plan
We track performance, monitor capacity, and identify early warning signs to prevent disruptions. This visibility strengthens planning, supports smoother operations, and keeps connectivity dependable for employees across department and location.
Proactive Oversight
We monitor network behavior continuously, identify activity early, and resolve problems before escalation. This oversight maintains stability, reduces frustration, improves continuity, and ensures your organization experiences reliable connectivity across operations.
Structured Tuning Plan
We refine configurations, adjust traffic flow, and remove bottlenecks that limit reliability. This optimization strengthens performance, reduces latency, prevents recurring issues, and ensures your network supports consistent workflows for employees.
Aligned Support Model
We maintain your environment based on organizational goals, coordinate improvements carefully, and support stability. This support strengthens reliability, improves performance, reduces downtime, and ensures your infrastructure remains ready.
Rising Demands Expose Network Weaknesses
Growing teams, added devices, and heavier cloud usage strain networks that were never designed for sustained workloads. Performance drops, unstable connections, and recurring interruptions start to affect productivity across departments, creating operational stress that slows progress and increases support needs.
Without structured oversight, hidden configuration problems accumulate and outdated hardware becomes a silent bottleneck. These issues create inconsistent access, inefficient workflows, and costly disruptions that hinder communication and daily responsibilities. Expert support restores stability by identifying weaknesses early and strengthening reliability across your entire organization.
Reliable Oversight Improves Everyday Operations
All -N- One Tech Solutions provides organized management that stabilizes your environment, strengthens performance, and reduces avoidable downtime. Our approach gives teams consistent access to the systems they depend on, while leadership gains confidence in predictable network behavior that supports ongoing objectives without interruption.
Through visibility, optimization, and aligned planning, we maintain performance across every location. Our structured management prevents recurring issues, supports long-term improvement, and ensures your network continues meeting operational demands as your business evolves and workloads increase across departments.

Why Businesses Choose Us
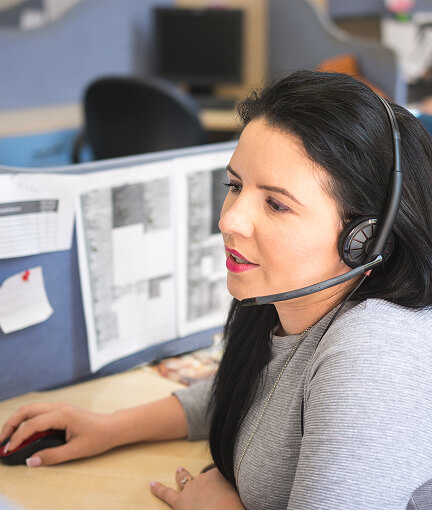
When it comes to cybersecurity, Houston businesses need more than a vendor who shows up after the damage is done. All -N- One Tech Solutions brings proactive, compliance-focused security to every client relationship, built on Nicole DeMoss's firsthand understanding of what small businesses actually face.
Proactive Security
Nicole DeMoss built All -N- One around prevention, not reaction. We identify and address vulnerabilities before they become incidents, keeping your systems, your staff, and your client data fully protected around the clock without causing disruption to your team.
Always-On Coverage
Threats don't follow a nine-to-five schedule and neither does our monitoring. Your network is watched continuously, with real-time response protocols in place so emerging threats are handled quickly before they have any chance to escalate into something worse.
Compliance-First Approach
Every security solution we deploy is mapped to the compliance requirements your industry demands. Houston businesses in regulated fields get infrastructure that satisfies auditors and protects client data without requiring a separate compliance project to get there.
No Generic Solutions
Your business has a specific environment, specific risks, and specific regulatory obligations. All -N- One assesses your actual setup and builds a security strategy around what your operations genuinely need, not a templated package designed for someone else entirely.
FAQs About Our Network and Infrastucture Services
What are the most common causes of persistent network instability issues?
Instability often results from outdated equipment, unmanaged devices, poor cabling, or unmonitored traffic patterns. These weaknesses create latency, interruptions, and inconsistent performance that affect staff, clients, and essential operational systems.
How can organizations effectively reduce recurring network congestion and bottleneck problems?
Bottlenecks are eliminated by optimizing configurations, replacing aging hardware, improving traffic flow, and monitoring usage trends. These steps strengthen performance and keep daily work responsive across all applications and communication tools.
What should a thorough network review include to ensure the best results?
An effective review examines configurations, hardware age, capacity limits, performance patterns, and security gaps. The findings guide improvements that strengthen reliability, reduce risks, and align infrastructure with operational goals.
How often should network infrastructure be properly updated or reviewed by organizations?
Most environments benefit from quarterly performance reviews and annual upgrade planning. This schedule ensures your infrastructure remains efficient, stable, and capable of supporting new demands without unexpected failures or performance drops.